
What clues reveal about a possible Windows 12
Editor’s note: This article is a translation of a German article by PC-Welt. It does not meet PCWorld’s standards and should not have been published. The first version did not include any source links...
Data analysis, big data, and business intelligence

Editor’s note: This article is a translation of a German article by PC-Welt. It does not meet PCWorld’s standards and should not have been published. The first version did not include any source links...

Maybe your gaming laptop doesn’t have enough storage. Or maybe you simply want to render your game library portable between systems. Rather than upgrade your internal storage — add a speedy external S...

An event-driven reconciliation pipeline on AWS ran into Lambda timeouts and DynamoDB hot partition keys when batch sizes grew. Learn how a hybrid Step Functions pattern (Lambda for small files, ECS Fa...

Private Kubernetes is the missing abstraction layer for enterprise hybrid cloud. Learn how a private Kubernetes platform enables portability, security, governance, and freedom from vendor lock-in acro...
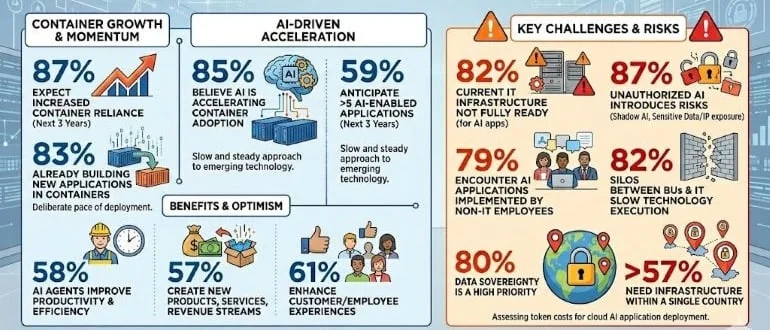
A global survey of 1,600 cloud, IT, and engineering executives published today finds a full 87% expect their organizations’ reliance on containers to deploy applications to increase over the nex...
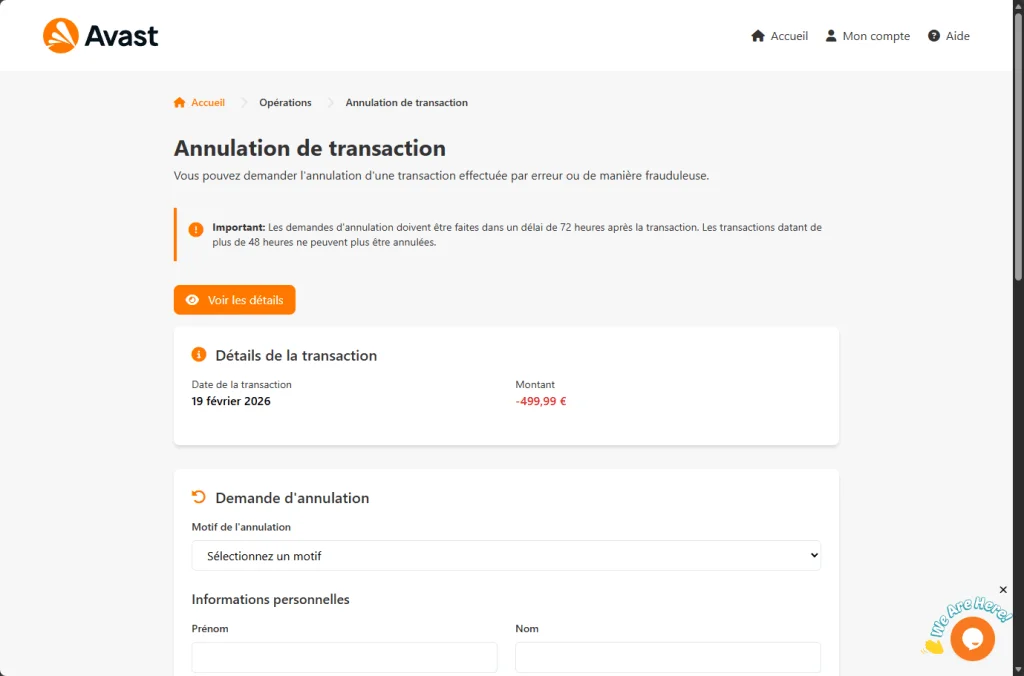
A convincing fake Avast site displays a €499.99 charge and promises a refund. Instead, it harvests your name, address, and full credit card details.
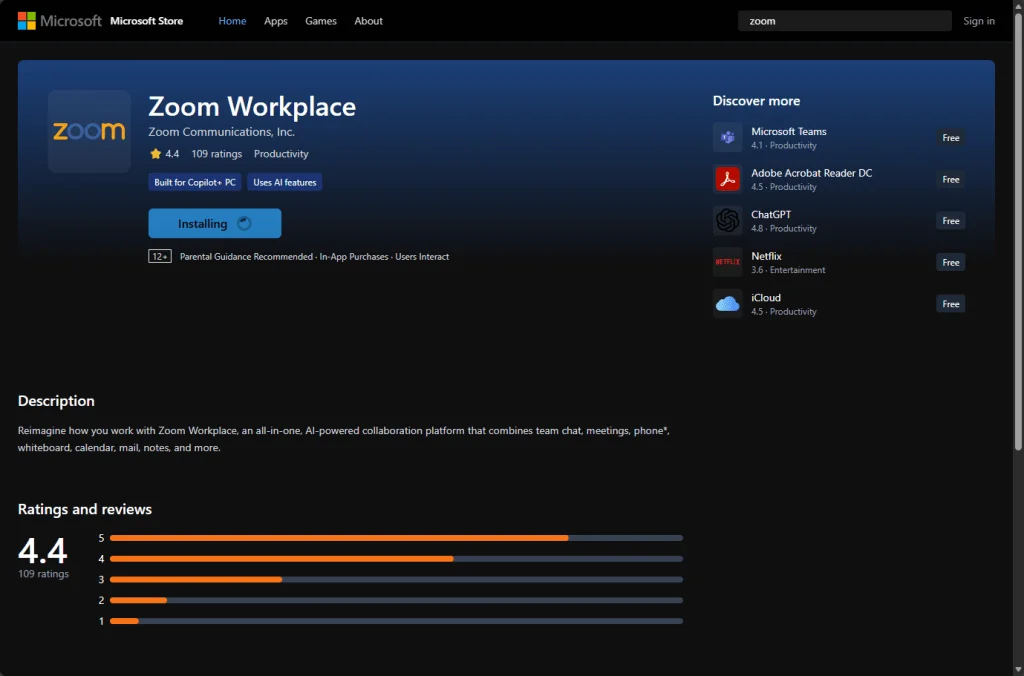
A fake Zoom meeting page looks real, triggers a bogus “update,” and silently installs a legitimate commercial monitoring product.
Los Angeles County sued the online gaming platform Roblox for its alleged failure to protect children from danger.
Ofcom and the Information Commissioner's Office respectively fined a US porn company and Reddit for failing to protect children online.
Unsealed court records reveal Instagram executives discussed explicit messages to teens years before a blur feature was introduced.
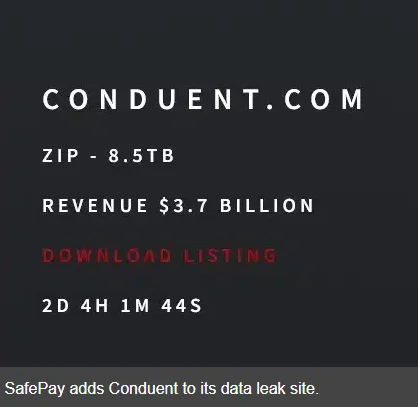
A third-party breach at Conduent now affects 25 million Americans—many never knew their data flowed through its systems.
APT stands for Advanced Persistent Threat. But what does that actually mean, and how does it translate into the kind of threat you’re facing?
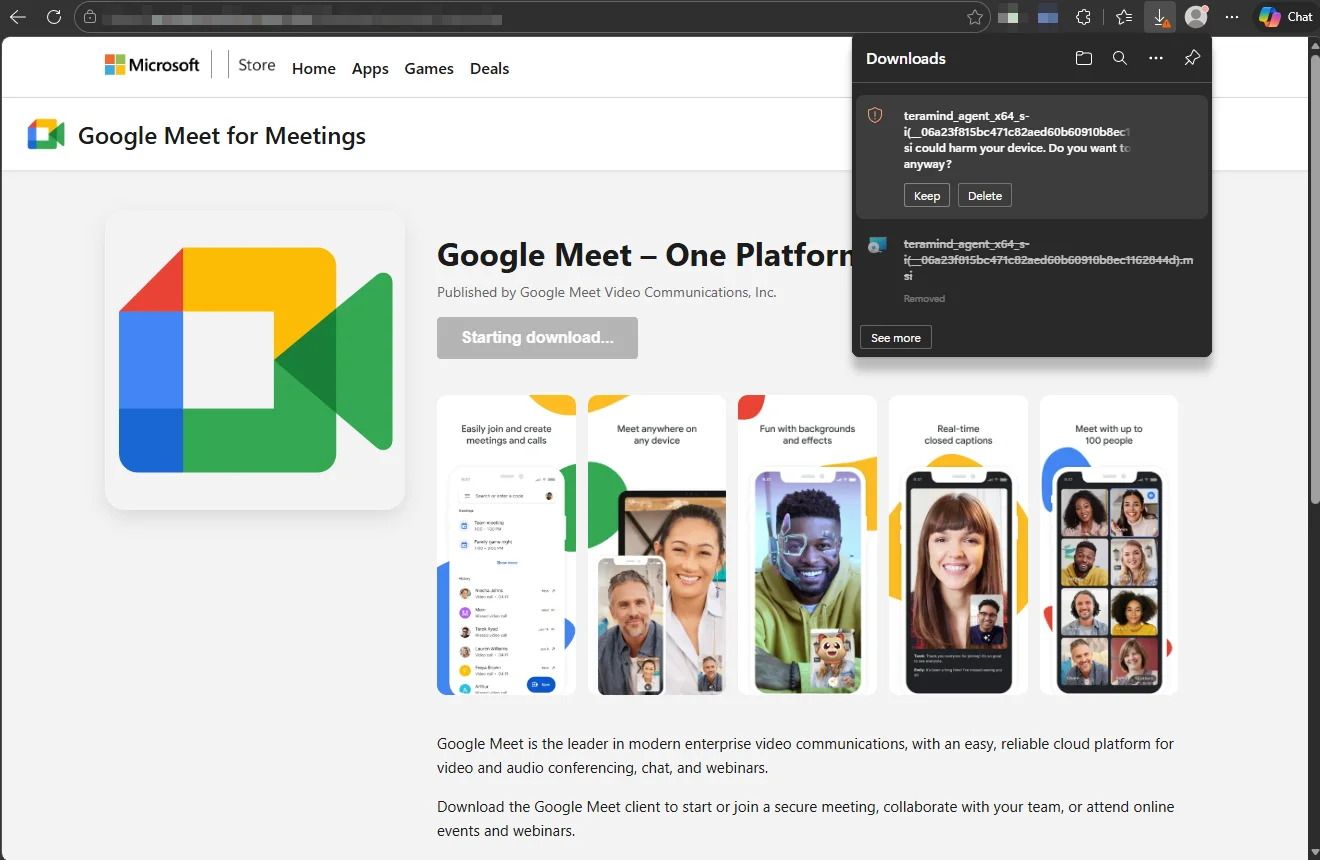
Attackers don’t always need custom malware. Sometimes they just need a trusted brand and a legitimate tool.
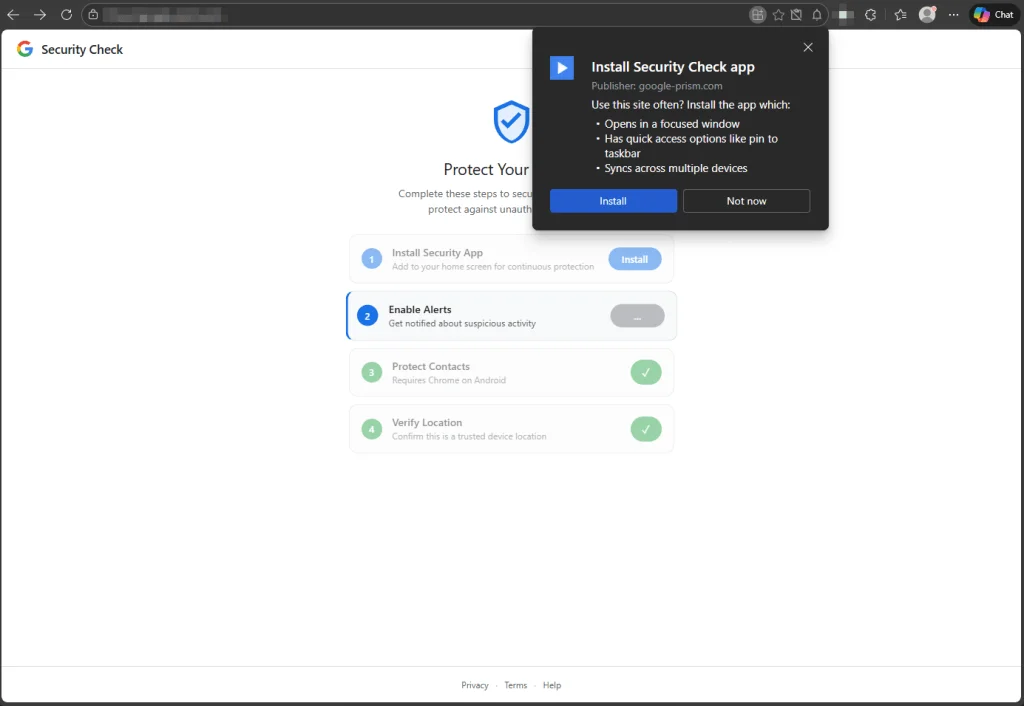
Disguised as a security check, this fake Google alert uses browser permissions to harvest contacts, location data, and more.
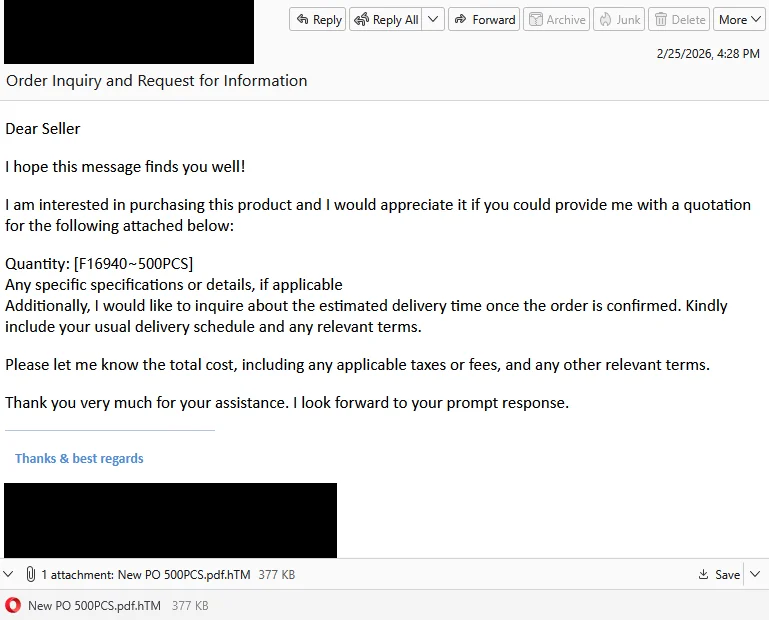
A fake purchase order attachment turned out to be a phishing page designed to harvest your login details.
As Samsung settles a lawsuit over how its smart TVs collect and monetize viewing data using ACR, here's how the rest of us can limit the data we're sharing.
Google has patched 129 Android vulnerabilities, including an actively exploited flaw in a widely used Qualcomm component.
Researchers have found that attackers are abusing OAuth to send users from legitimate Microsoft or Google login pages to phishing sites or malware downloads.
Reports of a "Great British Firewall" are exaggerated. And even if they wanted to, here's why it would be virtually impossible.

Saab is one of the top 10 defence primes in Europe and, while it previously invested in developing most of its technology in-house, the rapid advancement of AI and other defence and space technologies...