
WhatsApp will soon join the premium subscription club
More features for power users
Artificial intelligence and machine learning news

More features for power users

On an unsecured network—like public Wi-Fi networks—hackers can quietly insert themselves between you and the websites you visit. These “machine-in-the-middle” attacks (previously known as man-in-the-m...

We’ve been hearing about it for a while, and now it’s official: There’s a new entry-level MacBook in town. The MacBook Neo is small, cheap, colorful, and most importantly, available. Apple made some b...

At a glanceExpert's Rating Pros Super-clean interface and setup Affordable online storage Local and online backup Supports a wide variety of third-party online storage services Flawless in our testing...

Choosing a laptop doesn’t have to be a long, arduous process. But with so many models, price points, and flashy features, it often is. Will a bigger screen actually boost your productivity? Do you rea...

Editor’s note: This article is a translation of a German article by PC-Welt. It does not meet PCWorld’s standards and should not have been published. The first version did not include any source links...

Maybe your gaming laptop doesn’t have enough storage. Or maybe you simply want to render your game library portable between systems. Rather than upgrade your internal storage — add a speedy external S...

Crafting programs and apps with the help of AI agents has become quite the thing over the past few months, and Windows users just got a new “agentic” AI coding tool to play with. Roughly a month after...

Red Hat this week made available an enterprise-supported version of the open source Podman tool it created for developing, managing and running containers. James Labocki, senior director of product ma...

An event-driven reconciliation pipeline on AWS ran into Lambda timeouts and DynamoDB hot partition keys when batch sizes grew. Learn how a hybrid Step Functions pattern (Lambda for small files, ECS Fa...
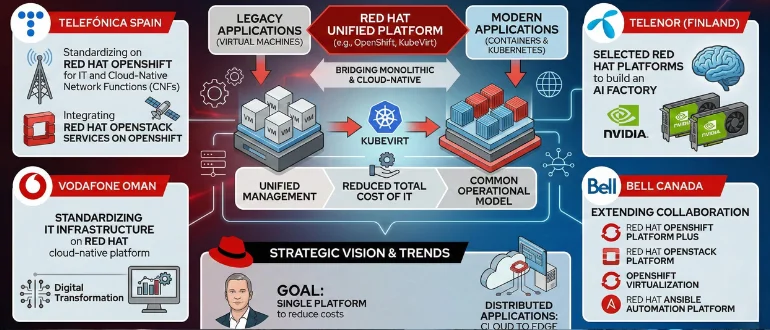
At MWC 2026, Red Hat announced partnerships with major telecommunications companies, including Telefónica and Vodafone, to adopt its platforms for cloud-native application development. This initiative...
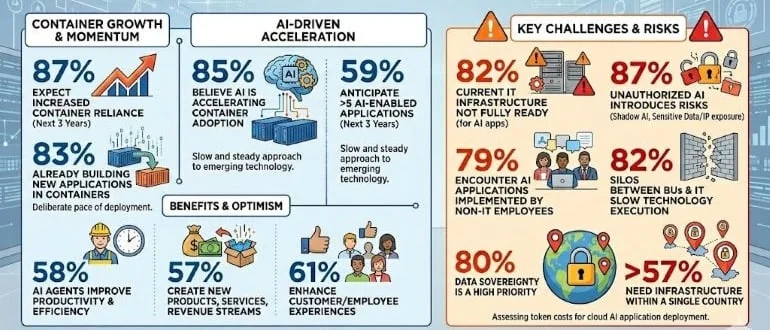
A global survey of 1,600 cloud, IT, and engineering executives published today finds a full 87% expect their organizations’ reliance on containers to deploy applications to increase over the nex...

Explore how an artifact access plane can improve Kubernetes platform performance, scalability, and security by standardizing how artifacts are governed and delivered, aligning with CNCF ecosystem init...
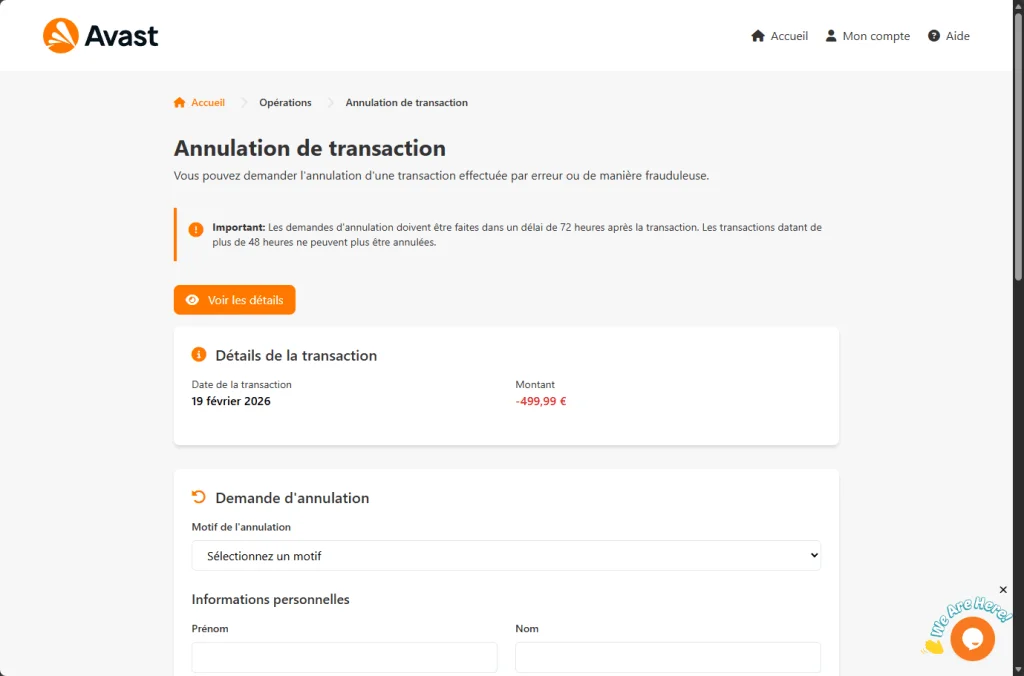
A convincing fake Avast site displays a €499.99 charge and promises a refund. Instead, it harvests your name, address, and full credit card details.
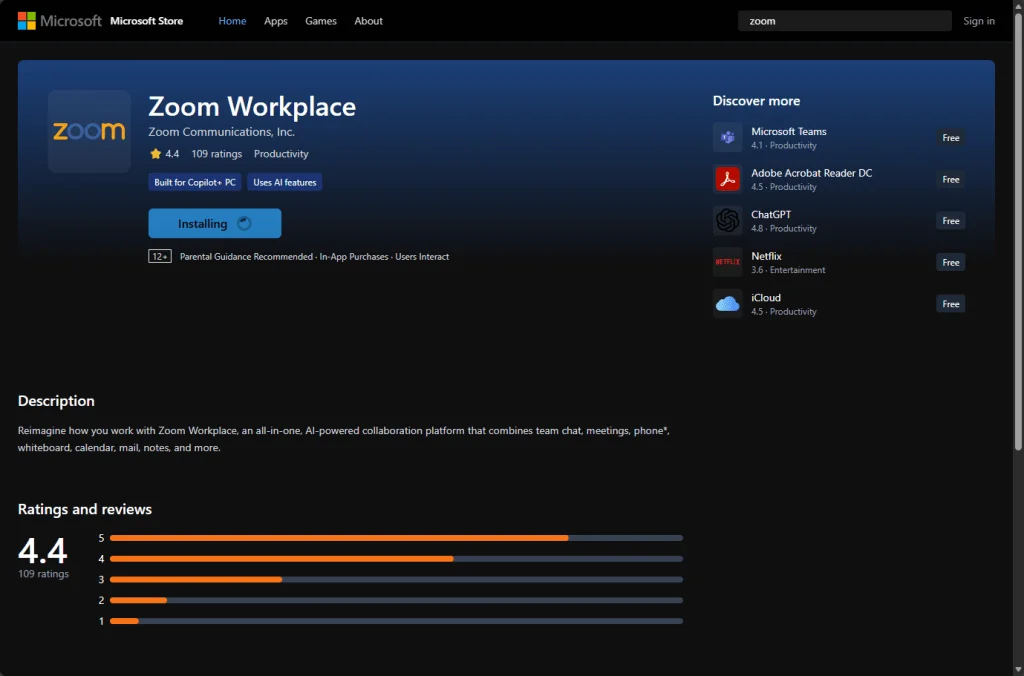
A fake Zoom meeting page looks real, triggers a bogus “update,” and silently installs a legitimate commercial monitoring product.
Los Angeles County sued the online gaming platform Roblox for its alleged failure to protect children from danger.
Ofcom and the Information Commissioner's Office respectively fined a US porn company and Reddit for failing to protect children online.
Unsealed court records reveal Instagram executives discussed explicit messages to teens years before a blur feature was introduced.
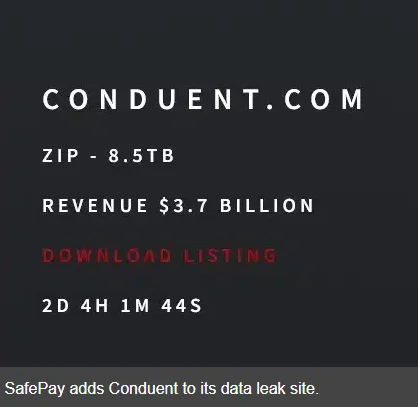
A third-party breach at Conduent now affects 25 million Americans—many never knew their data flowed through its systems.
APT stands for Advanced Persistent Threat. But what does that actually mean, and how does it translate into the kind of threat you’re facing?